WEEK 11
18 May 2018
Maintaining Access
(bypass firewall)
1. Protocol Tunneling Protocols (DNS Tunnel)
Method to encapsulate a protocol inside another protocol. The purpose of Protocol Tunneling is to bypass protection at target and stay lowkey in the network.
So to conclude, protocol tunneling means
you are not allowed to access XAMPP package, so try to create Secure Socket Tunneling Protocol (SSTP) first, after establish, put XAMPP package inside the protocol
The metaphor that can be used is North Korea and South Korea
North Korea does not allow people to go to South Korea. But if the people creating a tunnel without being known, they can secretly send ‘package’ or maybe travel to South Korea.
Ex : DNS2tcp. has 2 components server and client
2. Proxy Tools
Proxy is the middle server between 2 parties (client- server)
The purpose of proxy is to hide activities/actions is to secure real server behind proxy(reserve proxy).
In Indonesia, there are so many free open proxy available, we should not recklessly using free proxy, the proxy might be created by law enforcement / government in order to maintain our traffic or activities.
3. End-to-end Connection Tools
End to end connection create a connection between server-client|
The purpose of End-to-end connection is to transfer files from a remote server to client and to execute command in the remote server
Example of this tool is CryptCat, sbd, Socat
4. Create PHP Shell for Backdoor
PHP Shell is to create a small php code to allow execute OS command from browser. This will make sure the hackers can “maintain” their access with the malicious code inside the site without being notice. You can download the PHP Shell from this website http://r57.gen.tr/




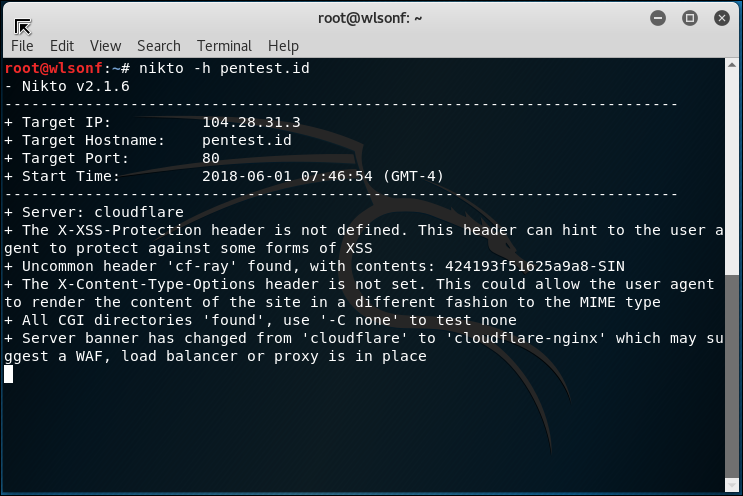


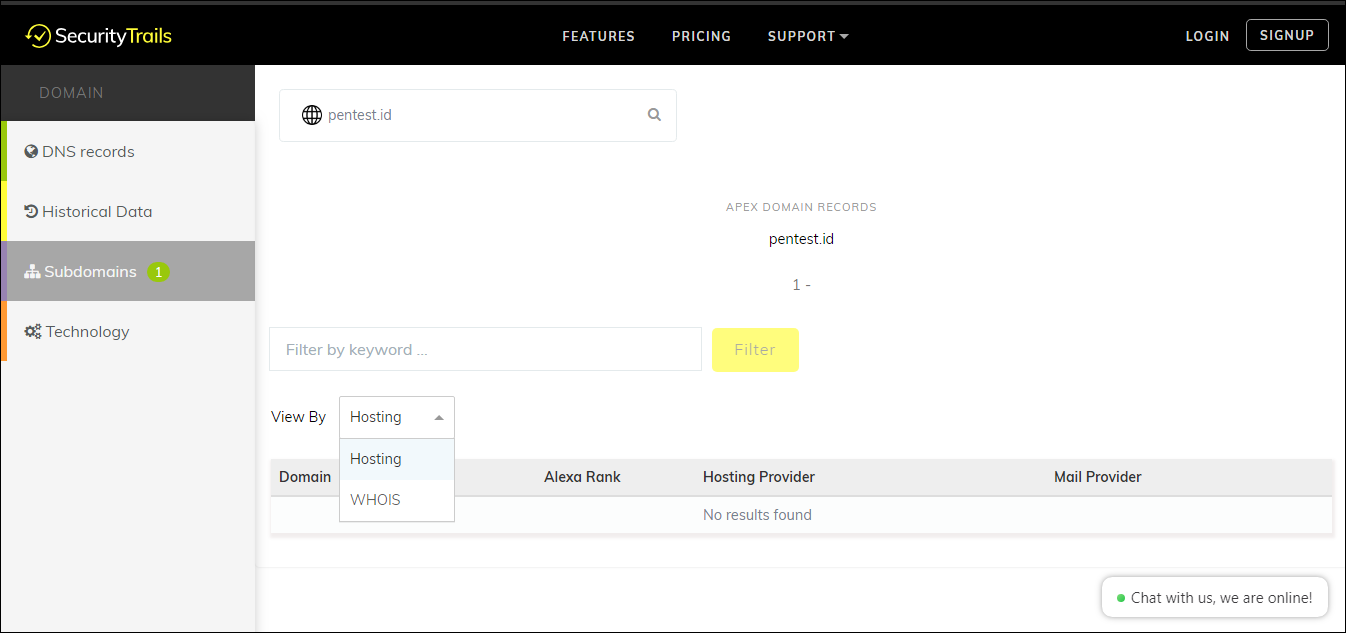
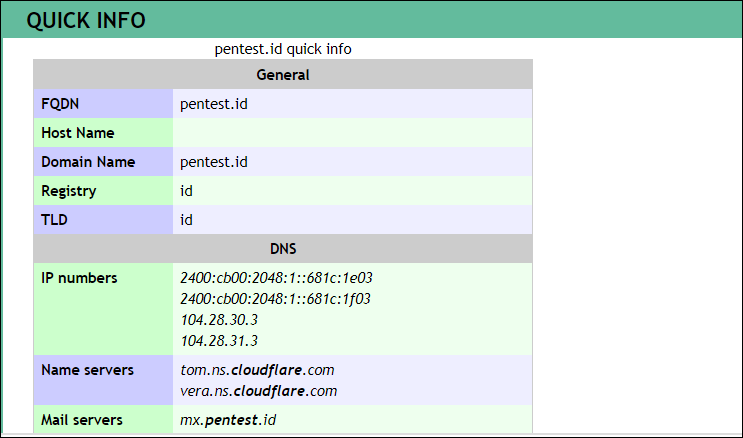
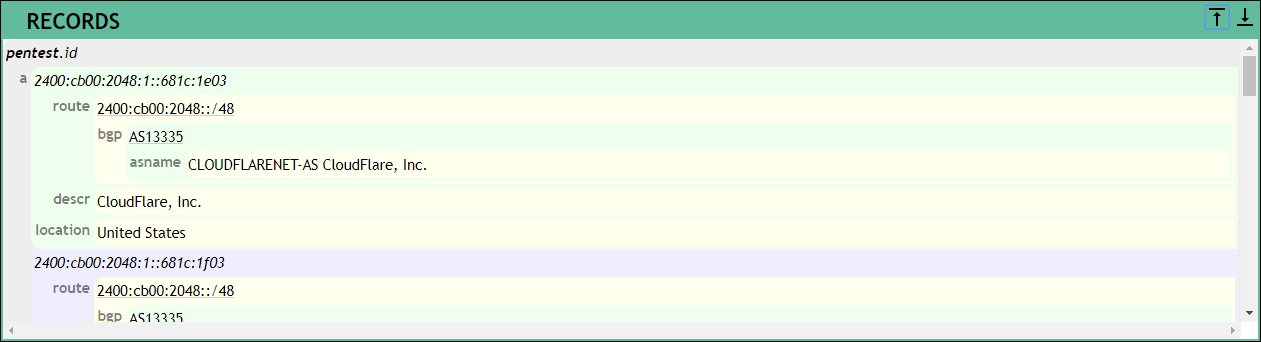
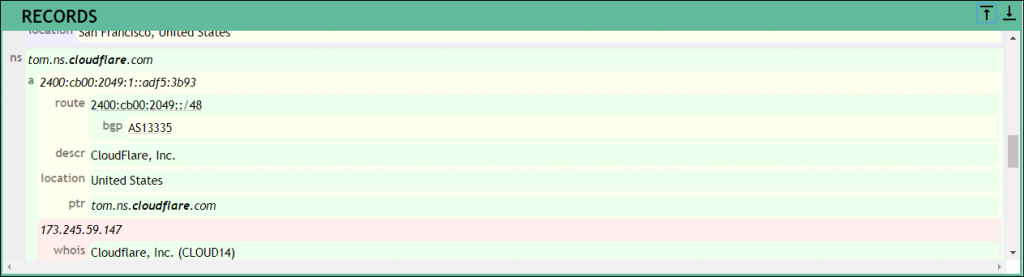
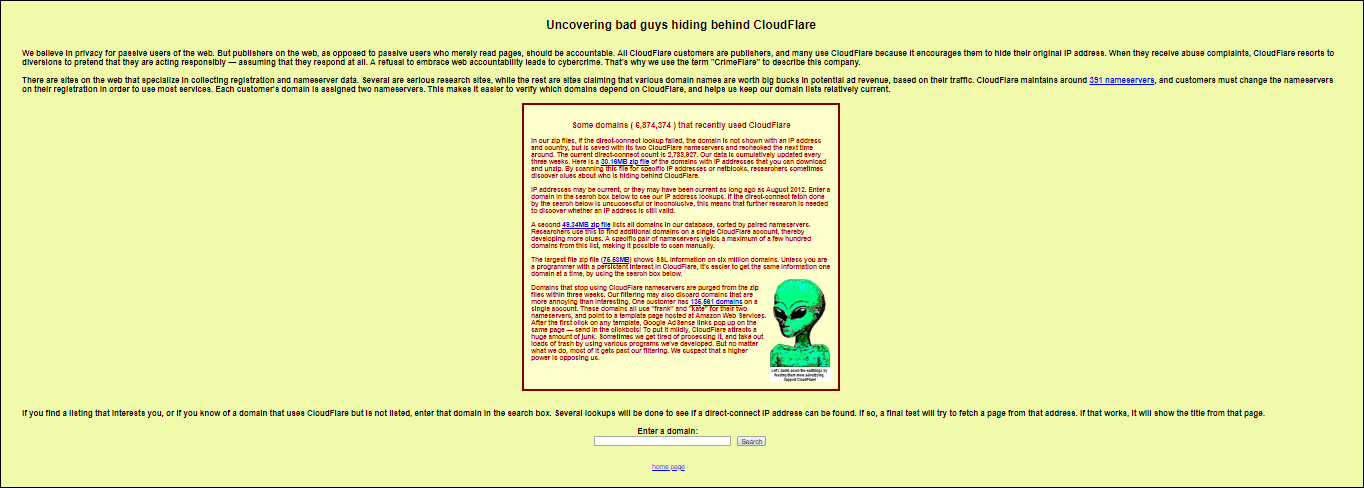
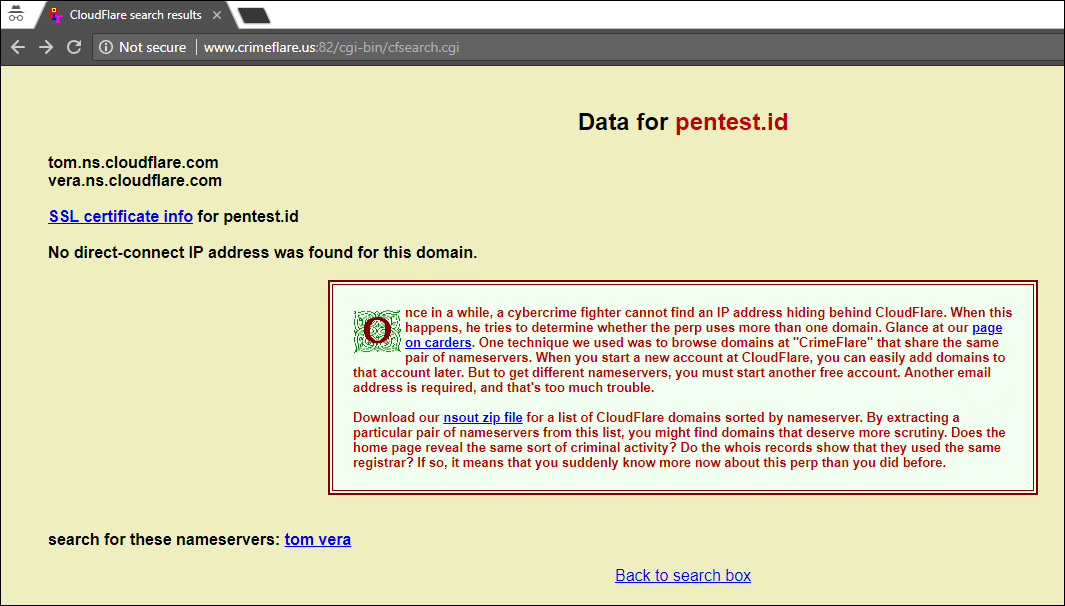
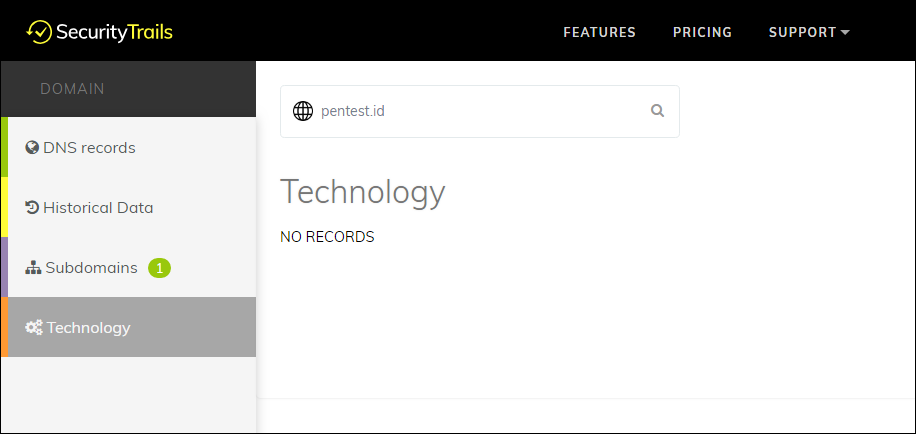 2.2 Robtex
2.2 Robtex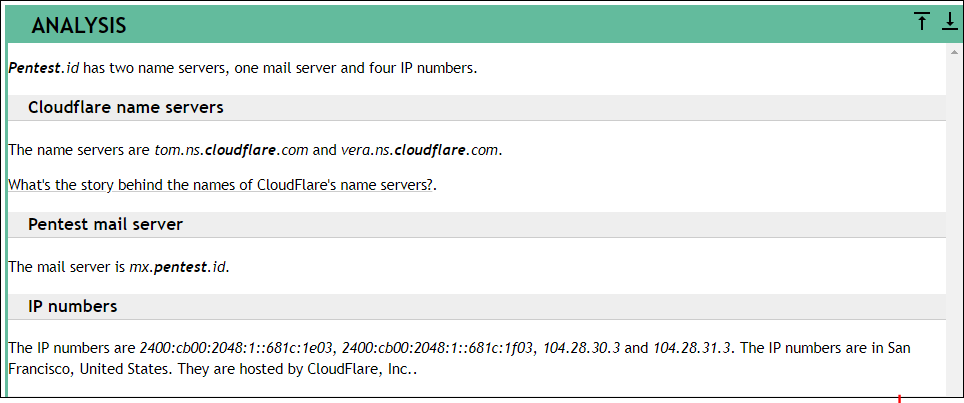









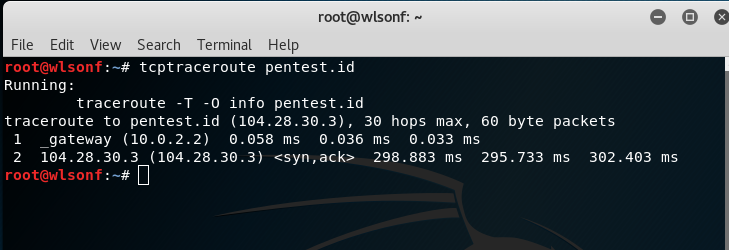
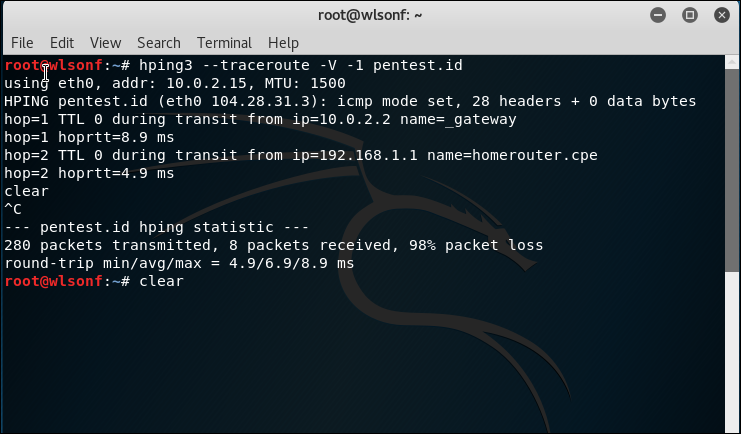
 4.7 Tcptraceroute command
4.7 Tcptraceroute command